Unit-2: Computer Software
Contents: Introduction to Software, Types of Software, Program vs Software, Computer Virus and Antivirus
Download the unit.
Introduction to Software
Among the two major components of a computer system, Software is one while Hardware being the other. Software refers to a set of computer programs and related data that provide the instructions for telling a computer what to do and how to do. It is a set of instructions that guides the hardware and tells it how to accomplish each task.
Hardware refers to the physical equipment that is necessary for performing various operations such as storing results and providing output to users in the desired form.
Types of Software
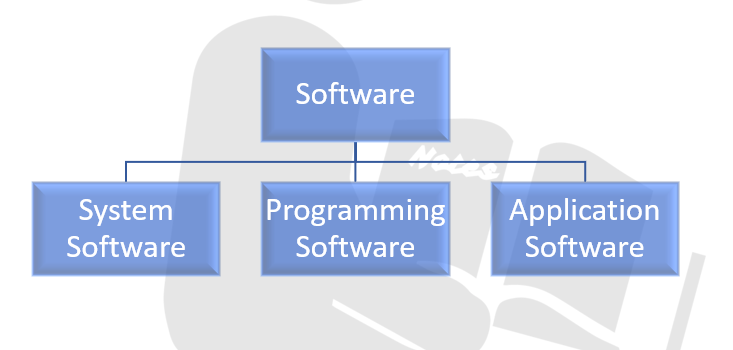
System Software
It is a type of computer software that is designed to operate the computer hardware so that the basic functionality and a platform for running application software are provided. Operating System and all other utility programs that manage computer resources at low level are system software.
Example: BIOS (Basic Input/ Output System) gets the computer system started after you turn it on, and it manages that data flow between the operating system and other attached devices such as hard disk, video adapter, etc. System utilities such as the disk defragmenter and system restore are also system software.
Programming Software
It includes tools in the form of programs or applications that software developers take in use to create, debug, maintain and support other programs and applications. Compiler, debugger, interpreter, linker and text editor are the parts programming software.
1. Compiler
They convert a high level language program into a low-level language program.
2. Assembler
They convert an assembly language program into low-level language programs.
3. Interpreter
It processes high-level language line by line and simultaneously produces low-level programs.
4. Linker
Most low-level languages allow the developer to develop a large program containing multiple modules. Linker arranges the object code of all the modules that have been generated by the language translator into a single program.
5. Debugger
It is a software that is used to detect the errors and bugs in programs. It locates the position of errors in the program codes.
6. Text editor
It is a program that allows the user to work with texts in a computer system. It is used for documentation purpose and enables us to edit information present in an existing document or file.
Example: C, C++, C#, BASIC, Java, Python, etc.
Application Software
It is a program of a group of programs designed for individual users. It allows end-users to accomplish one or more specific non-computer related task.
Example: Word processor, presentation software, data management system, desktop publisher, web browsers, etc.
Program vs Software
Software is the superset of programs in which one or many programs are executed sequentially or simultaneously to perform a particular job. It is the end product of a set of programs.
Example: MS-Excel
A program is a combination of lines of codes which takes input works on instruction on a computer to generate output. A program is the group of instructions which when performed will generate a logical output.
Example: addition or subtraction operation in MS-Excel
Summarizing, the program is a set of instructions that are executed by a computer, whereas software is a set of programs.
Example: the calculator is a software whereas addition, subtraction, etc. are set of programs that exist in the calculator
Computer Virus ad Antivirus
Computer Virus
A computer virus is a set of malicious code or program written to alter the way a computer operates. It is usually designed to spread from computer to computer. A virus operates by inserting or attaching itself to a legitimate program or document support macros in order to execute the codes.
A virus has the potential to cause unexpected or damaging effects such as harming system software by corrupting or damaging data. Once a virus successfully attaches itself to a program, file or document, the virus will remain dormant until circumstances cause a computer to execute its code. In order for a virus to infect any computer, the infected program has to be run in order for the code to be executed.
Signs of Computer Virus
1. Frequent pop-up windows
2. Changes your homepage
3. Mass email being sent from your email account
4. Frequent crashes
5. Slow computer performance
Different types of Virus
1. Boot sector virus
This type of virus can take control when you start or boot your computer. It spreads by plugging Flash drives.
2. Web scripting virus
This type of virus exploits the code of web browsers and webpages. It spreads through infected webpages.
3. Browser hijacker
This type of virus hijacks certain web browser functions and might automatically be directed to unintended sites.
4. Resident virus
This is the general type of virus that inserts itself in a computer system memory. A resident virus can execute at any time when the operating system loads.
5. Direct-action virus
This type of function comes into action when you execute a file containing a virus otherwise it remains dormant.
6. Polymorphic virus
A polymorphic virus changes its code each time the infected file is executed. It does this to invade antivirus.
7. File infector virus
This common virus inserts malicious code into executable files. i.e. files used to perform certain functions or operations on a system.
8. Macros virus
Macros virus are written in some macro language used for a software application. Such virus spread when you open an infected document often through an email attachment.
Antivirus
Antivirus is a type of program designed and developed to protect a computer from malware like computer virus, worm, spyware, botnets, boot-kits, keylogger, etc. Antivirus function to scan, detect and remove such viruses from the computer. Most antivirus incorporates both automated and manual filtering abilities. Instant scanning option may check files downloaded from the internet, disks that are embedded into PCs and files that are made by software installers.
Features of Antivirus
1. Default deny protection
It is implemented to prevent the entry of suspicious files by default.
2. Auto sand-box technology
A virtual environment where suspicious and unknown files are secluded and run to check for any malicious activity without interfering the normal operations.
3. Containment technology
It validates and authorizes the programs that are executable and ensure that processes are running without affecting the regular operation of the system.
4. Host intrusion protection system (HIPS)
It terminates any malicious activity once found. This prevents malware from infecting the operating system, registry keys, personal data or the system memory.
